
JFrog Artifactory: how to secure binaries in the AI era
The explosion of AI-generated code is creating a security crisis that traditional manual approaches simply ca...

The explosion of AI-generated code is creating a security crisis that traditional manual approaches simply ca...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

Spanish police on Saturday arrested three individuals suspected of hacking. They allegedly carried out activi...
The aftermath of Friday's global disruption caused by a CrowdStrike Falcon sensor is becoming clearer. On Sat...

Hackers are using phishing to mitigate the problems caused by the CrowdStrike update. In particular, attacks ...

CrowdStrike has addressed the cause of the outage. "The issue has been identified, isolated and a fix has bee...

Tech giants and AI developers want to achieve better security for AI applications with the Coalition for Secu...


Several critical services went down last night after security company CrowdStrike tried to update its systems...

The list of companies whose data has been captured in the massive data theft from Snowflake environments keep...
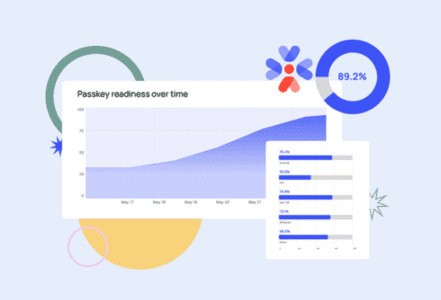
1Password will actively help developers determine whether their applications' end users can already switch to...
