
Is 46% of your AI-generated code vulnerable?
As AI coding assistants become ubiquitous in enterprise development, a concerning statistic has emerged: 46% ...

As AI coding assistants become ubiquitous in enterprise development, a concerning statistic has emerged: 46% ...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

The German IT services company Bitmarck has been feeling the effects of a cyberattack. Its internal systems r...
The U.S. Department of Justice was aware of the SolarWinds hack earlier than it had previously admitted. Susp...
This week Amazon announced that it was making its new AWS Verified Access service generally available. The ex...

The tech giant says it cancelled thousands of developer accounts and blocked over a million apps from reachin...

The 2023 RSA Conference featured announcements from all over the cybersecurity sector. We're presenting a rou...

API security company Noname Security continues to find partners. This time it is announcing a partnership wit...
Artificial intelligence is going to shake up security. RSA CEO Rohit Ghai stated at RSA Conference that it is...

The new features are designed to conform with the latest US federal guidelines for cybersecurity. This wee...
The attack by a North Korean hacker group that led to the 3CX breach has had ripple effects in the European e...
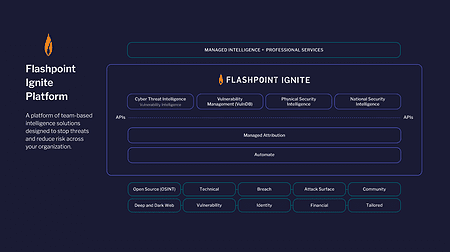
Security vendor Flashpoint is launching a new threat detection platform. With Ignite, users should be able to...