
Security

Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.
Timeline
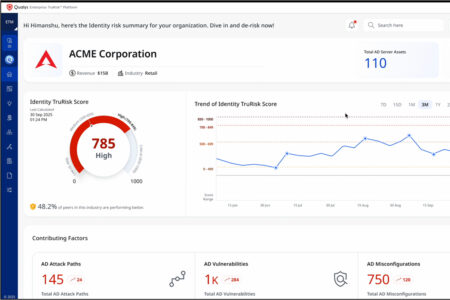
Qualys expands ETM security platform with identity security and better insight into threats
Qualys is expanding its Enterprise TruRisk Management (ETM) platform with three new AI-driven capabilities de...

NTT DATA and Fortanix join forces to secure sensitive data
NTT DATA and Fortanix announce a global partnership to help companies transition to post-quantum cryptography...
SonicWall VPN accounts compromised with stolen login credentials
Security researchers are warning of a large-scale campaign. Attackers compromised more than 100 SonicWall SSL...

Emergency patch for vulnerability in Oracle E-Business Suite
Oracle released an emergency patch this weekend for a critical vulnerability in E-Business Suite. This softwa...

Data of millions of Qantas customers published months after hack
Australian airline Qantas has confirmed that the personal data of 5.7 million customers has appeared online f...

Apple doubles highest bug bounty reward to $2 million
Apple has announced an update to its Apple Security Bounty program. The company is doubling the maximum rewar...

Dutch restrict Nexperia to keep its chip secrets outside of China
For one year, Nexperia is only allowed to take decisive action when the Dutch government allows it. The Minis...

More than 100 companies likely affected by Oracle hack
Security researchers at Google say that more than 100 organizations are likely to have fallen victim to a lar...

Fifty years of security by design: why isn’t it working?
Professor Bibi van den Berg on missed opportunities

Salesforce refuses to give in to extortion after SalesLoft data breach
Salesforce has informed customers that it will not pay ransom to hackers threatening to publish stolen custom...