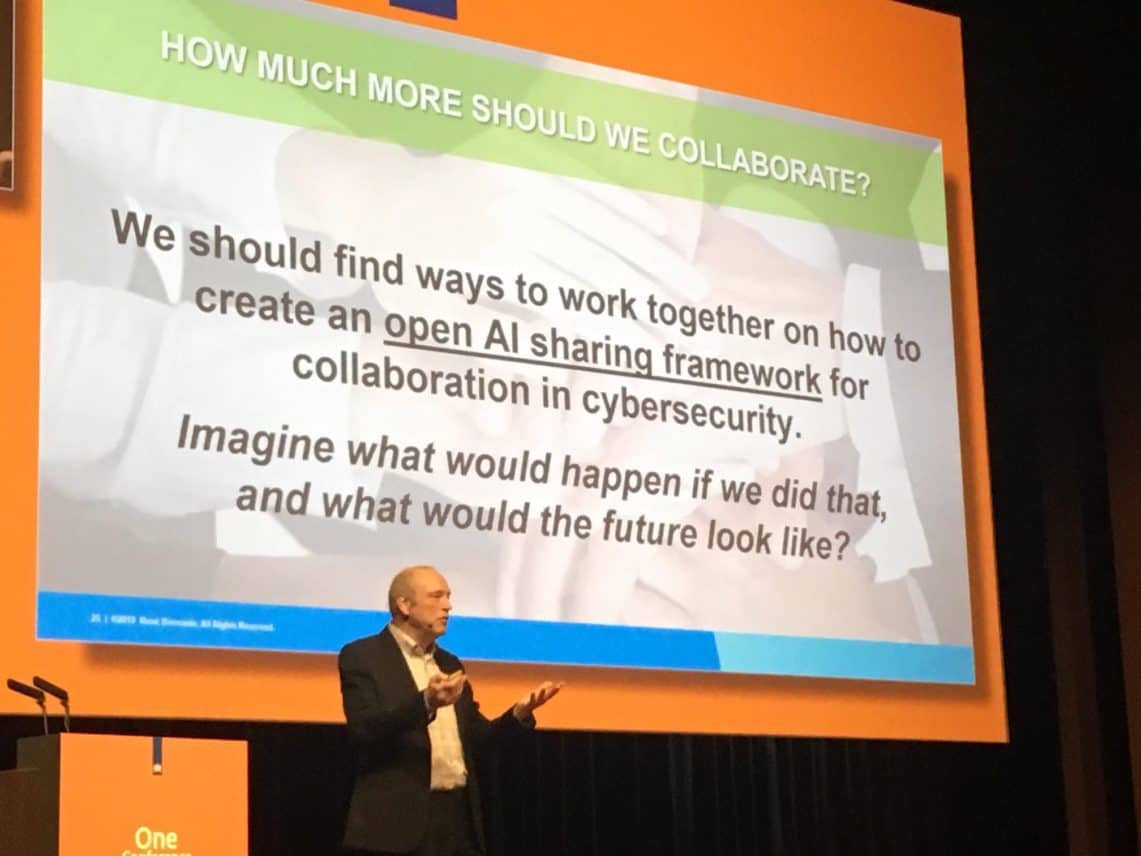
Algorithms and methodologies for artificial intelligence (AI) and machine learning are becoming increasingly important in cybersecurity. However, more cooperation between the various stakeholders is needed in order to unlock the full potential of these technologies. By placing them in a public AI Framework, for example. Techzine spoke about this with Executive Vice President for Strategic Accounts René Bonvanie at Palo Alto Networks during the One Conference 2019.
Within the cybersecurity community, the thesis is still too often that the ‘bad guys’ cannot be won. According to former Cisco CEO John Chambers, there are only two types of companies: those who know that they have been hacked and those who do not yet know. This has become a popular statement within the cybersecurity industry. It is also often said that companies should not only ask themselves if they will ever be hacked, but when.
These dark messages were recently heard during the annual cybersecurity conference One Conference of the Ministry of Justice and Security/National Cybersecurity Centre (NCSC-NL) in The Hague. Here, too, people warned that time is running out, and that if we do not act quickly, the fight against malevolent actors, be they professional criminals or nation state actors, is in danger of being lost.
Fortunately, there are still optimists in this world who believe that the battle against the ‘bad guys’ can be won. These kinds of thoughtsoften come from the industry that is working hard to make the digital domain a little safer every day.
New technology
The industry is currently busy with deploying the latest technologies in the cybersecurity domain, such as AI and machine learning. According to Palo Alto Networks, these are the best technologies that can currently be used against cybercriminals.
The main reason for this is that AI and machine learning can be used more effectively and above all more preventively on a larger scale. This is instead of waiting patiently for incidents to occur and then reacting to them. It is, therefore, still possible to prevent rather than just cure.
However, Bonvanie sees that too little is currently being achieved in this area. There are still too many different suppliers, tools and alerts, and too much manual work has to be done to cope with the enormous growth in the number of attacks. And this is certainly not enough. Think of all the fileless attacks, automated attacks and attacks on the (public) cloud environments that are coming towards us.
Make ‘old’ technology ‘new’ again
All this means that the current security landscape is still too often focused on solving rather than preventing it. Also, often from a commercial point of view, there is still too little cooperation. That’s why it has to be completely different, says Bonvanie. According to him, this requires a new thought step.
First of all, it must be clear that all threats and alerts can no longer be solved by humans. They are often too complex for that, and there is simply a lack of enough security experts. This means that the problems surrounding cybersecurity should actually be solved in an automated manner. This means that it is not 6600 security specialists who are plodding day in, day out, but servers who use large-scale computing power to tackle these problems and come up with solutions in the shortest possible time. This goes without saying, with the use of AI and machine learning.
Palo Alto sees artificial intelligence and machine learning as technologies that have been around for quite some time, about 20 to 30 years. Many older algorithms and methodologies are still used today within cybersecurity. What matters most now is the way in which these technologies are used and what is needed to achieve this.
Basic conditions for automation
There have to be good models for security specialists to work with. In this way, threats can be prevented and resolved automatically and on a large scale. This requires a number of basic conditions: the availability of large amounts of data, the ability to use many algorithms and methodologies and, most importantly, a great deal of cooperation in these two areas.
In concrete terms, algorithms can be applied to the collected data and metadata. This should ultimately result in models that can predict whether certain actions on networks or software are good or malicious. These predictions are automated, which makes it easier to predict which actions any hackers will take or which defensive steps need to be taken to prevent the attacks. Automation enables this to take place on a scale that makes it possible to tackle the numerous cyber threats in a more preventative manner.
Dealing with intellectual property
The Palo Alto director realizes that it is difficult for the various stakeholders to make their own developed intellectual property publicly available. This way, others can also benefit from it.
According to him, the important thing is that they make the developed algorithms and methods publicly available, and that they can ‘just’ do what they want to do with them in commercial products. Not only the developers of these algorithms and methodologies, but also other security stakeholders.
Because of the legal reasons surrounding patents and intellectual property, reference must be made to the original developer(s). In turn, suppliers should be encouraged to develop more algorithms themselves and to share them.
Example of working method
Palo Alto itself already works in this way and makes algorithms and methodologies publicly available. Particularly at universities, governments and related institutions. This without asking for anything in return. In this way, the company builds trust and this trust is eventually rewarded by the fact that these agencies provide the security specialist with new information about algorithms and methodologies. Palo Alto can then further develop and provide feedback, but can also use the information to refine its products further. This, in turn, creates new possibilities that can be shared.
Independent organisation
The proposed Open AI Framework must be accommodated in an independent organization, says Bonvanie. Think of a platform like Mitre att&ck where cybersecurity data is shared and tested. Another example is Europol, where data is received, but it is also examined whether this has been done in a fair manner. The commercial interest must also be subordinate to the value that cybersecurity professionals attach to the shared information. Therefore, it must be a non-commercial organisation, but one that is sponsored in a very transparent manner by industry and governments. Furthermore, the Palo Alto director considers it important that there is strong cooperation with the academic world; the place where future research must and will take place.
In the meantime, this framework has been the subject of considerable consultation with various universities, including all technical universities in the Netherlands. In addition, consultations are taking place within the Cyber Threat Alliance partnership and with important fellow companies of Palo Alto in the field of cybersecurity, such as Cisco.
Objections
There are also many objections to such a framework. Think of the idea that it makes it very easy for hackers and other malicious parties to develop advanced methods of attack and to abuse the shared information. Bonvanie’s answer to this is that he already assumes that opponents know what he is going to do, but that it is precisely through cooperation that the ‘good guys’ will be stronger.
No good cooperation now either
Another important argument against a framework that is set up in this way is that the security industry is not cooperating well at the moment either. The industry is still too fragmented, keeps developments in the field of AI and machine learning to itself and is also under pressure from social and macro-economic developments. These include the various trade wars and – in Europe – the Brexit. The more fragmented the security industry is, the more it benefits its opponents.
Good response to opponents
According to the Palo Alto director, the cooperation he proposes with the Open AI Framework is a good answer to how the opponents are doing. According to him, there is already a lot of cooperation in the development of attack methods. By working together preventively and defensively within the industry, an even better answer can be given to this question, and resistance will be strengthened. Furthermore, sharing information about algorithms and methods stimulates innovation and ultimately benefits the entire economy, he tells us. The Open AI Framework can, therefore, become a win-win development in many respects.
Curious about the next steps
With his call for an Open AI Framework for sharing algorithms and methodologies that AI and machine learning use for cybersecurity, the Palo Alto executive has dropped an interesting bombshell. Certainly because he himself has indicated to us that the security industry really needs to take action.
There has been talk of joint action for years, but little has gotten off the ground in this area. In his view, the industry is still too fragmented. Now, cyber threats can be combated more effectively with artificial intelligence and the scale and computing power of the public cloud. This makes it easier to combat cyber threats, and it is therefore important that cooperation will be stepped up.
