Researchers at the Technical University of Berlin discovered serious security risks in IoT applications on 5G networks.
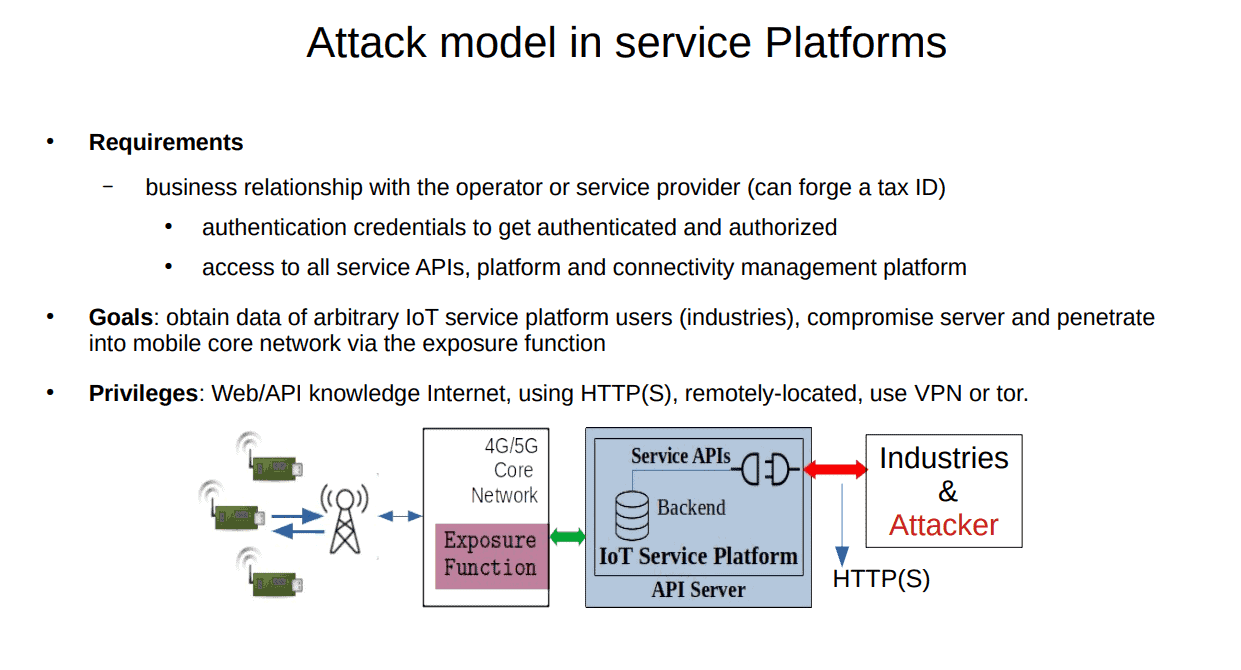
According to the researchers, the vulnerabilities primarily originate in the APIs with which operators help customers make IoT data accessible to developers. These APIs are broadly used for web services, but have recently started being deployed by operators due to their capabilities for 5G networks.
In their research, Altaf Shaik and Shinjo Park of the German Technical University and FastIoT found that the 5G IoT APIs of ten major telecom operators contain common and important vulnerabilities. Hackers can exploit these vulnerabilities for unauthorized data access and direct access to IoT devices located on the network.
Operators provide nearly complete platforms for 5G and IoT applications, which makes it relatively easy for hackers to exploit them. The packages that come with these platforms consist of all kinds of information and APIs. According to the researchers, not all IoT platforms are specified for the 5G standard. Furthermore, the implementation often leaves much to be desired. The platforms are typically mere extensions of existing 4G networks, which increases the attack surface.
Research results
The researchers used data-only SIM cards from the investigated operators for IoT applications. The analysis uncovered various vulnerabilities in the design of 5G networks. The area of authentication was error-prone and lacked access control tools. The APIs investigated exposed SIM card identifiers, SIM card secret keys, the identity of the SIM card’s customer, and payment information. The researchers were able to access large user data streams by sending commands.
The researchers notified the mobile operators. The operators announced they will correct the errors. However, the researchers indicate that the quality of IoT platforms for 5G still varies greatly. Some platforms are more mature in their security than others. Some platforms reportedly adhere to old, poor security technologies and principles. The researchers expect to find more 5G vulnerabilities in the near future.
Tip: BT increases standalone 5G speeds with carrier aggregation
