
Rubrik SAGE: using AI to govern agentic workforces
As agentic AI systems move from proof-of-concept to production, enterprises face a security challenge: how do...

As agentic AI systems move from proof-of-concept to production, enterprises face a security challenge: how do...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

The French job seeker agency Pôle Emploi has been hit by a data leak in which the data of 10 million French ...

Hackers managed to penetrate Econocom's systems last weekend. The investigation into the event is ongoing. ...

Malware is increasingly being spread through fraudulent ads, a practice known as malvertising. Full-page prom...

Researchers at Zscaler ThreatLabz have discovered a new infostealer family for Windows systems: Stact Stealer...

The British 18-year-old alleged mastermind behind the notorious Lapsus$ hacking attacks has been found guilty...
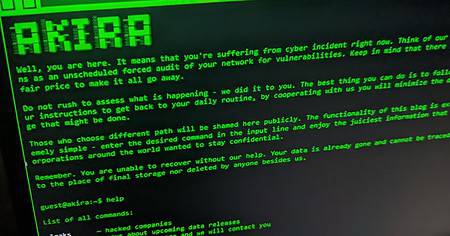
Security providers, including Sophos and SentinelOne, note that the Akira ransomware is increasingly targetin...

The TP-Link Tapo L530E smart lamp not only provides light, but also allows hackers to steal WiFi passwords vi...

Ivanti has patched a vulnerability in its software for the third time within a month. This time it involves a...

SentinelOne is looking at a possible sale with investment bank Qatalyst Partners. Ever since the upswing that...

WinRAR users, without a patch, are vulnerable to CVE-2023-40477, a serious software flaw. The bug allows atta...