A problem in the supply chain caused the vulnerability to go undetected for nearly six years. Intel and Lenovo have no plans to release a fix, as the affected hardware is no longer supported.
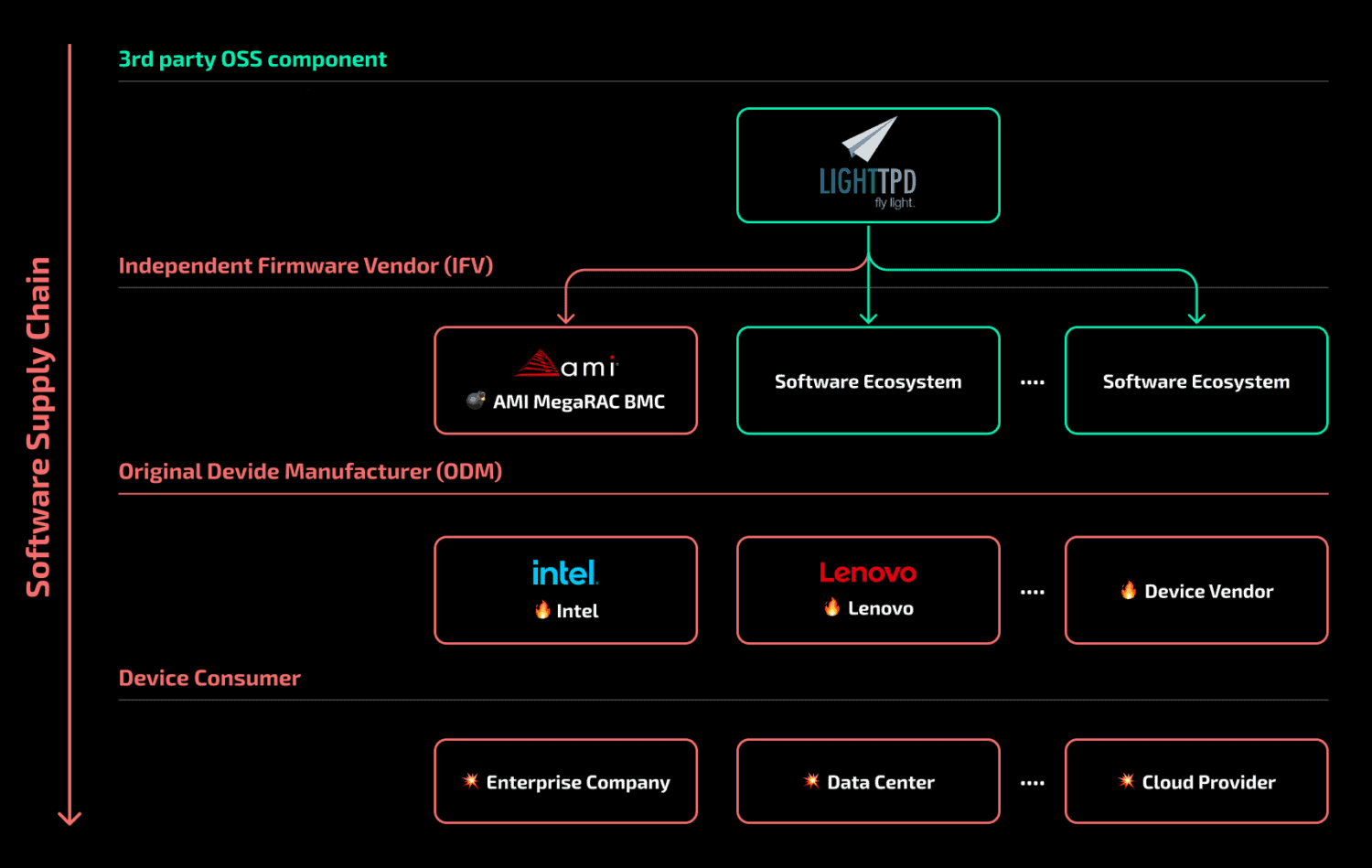
So state security researchers at Binarly. In addition to Intel and Lenovo, Binarly lists Supermicro as an affected vendor. The vulnerability allows malicious parties to gain access to sensitive information. It is located in the open-source software lighttpd, which is present in Motherboard Management Controllers (BMCs).
These BMCs are tiny computers on servers’ motherboards that are used to manage servers remotely. Administrators can use them to reinstall operating systems and uninstall apps, for example. However, many BMCs use lighttpd to allow remote administrators to access servers with HTTP requests.
Six years ago, the makers of lighttpd released a new version. This version fixed vulnerabilities that could be exploited to perform malicious activity on memory functions. However, there was no explicit mention of a “vulnerability” at the time, nor were there any CVE vulnerability numbers listed.
Impact
Binarly sees that server vendors continued to produce BMCs with the vulnerable version of lighttpd. “All these years, it was present inside the firmware and nobody cared to update one of the third-party components used to build this firmware image,” the security researchers said.
To BleepingComputer, Binarly states that data show at least 2,000 servers were affected. In reality, the impact is estimated to be much larger. Among them are Intel, Lenovo, and Supermicro systems. Hardware from Intel sold as recently as last year has been affected. Intel and Lenovo have no plans to develop a solution, due to no longer supporting the affected hardware. Supermicro’s affected servers are still supported.
On a side note, the lighttpd vulnerability is classified as moderate. Only a working exploit for a more severe vulnerability will benefit a hacker.
Tip: xz backdoor shows how vulnerable open-source is to hackers playing the long game
