
Rubrik SAGE: using AI to govern agentic workforces
As agentic AI systems move from proof-of-concept to production, enterprises face a security challenge: how do...

As agentic AI systems move from proof-of-concept to production, enterprises face a security challenge: how do...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

Fortinet is again warning of a critical vulnerability, this time in FortiOS SSL VPN. The vulnerability enable...

Security researcher Stacksmashing managed to crack Microsoft's Bitlocker encryption in 43 seconds. To do so, ...

Commercial spyware vendors appear to be the largest developers of zero-day vulnerabilities. Through these vul...

Last year, more than $1.1 billion (€1 billion) in ransom payments were made following a cyber attack. This ...

The vulnerability allows hackers to execute code early in a device's boot. Virtually all Linux distributions ...

Fortinet's FortiSIEM solution has been hit by two vulnerabilities rated most critical at 10. The vulnerabilit...

Canon has recently fixed some long-known vulnerabilities in its own printers via a patch. Printers still appe...

Akamai recently introduced the Content Protector tool. With it, websites can be protected from scraper bots t...

The Dutch Ministry of Defense discovered in 2023 that it was being spied on by China via malware. The damage ...
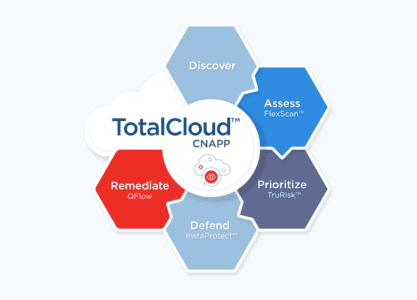
A major upgrade to Qualys TotalCloud should ensure that all cloud vulnerabilities are easily visible together...