A recent mass infection of nearly 11,000 websites has been discovered by security firm Sucuri. The websites in question use WordPress as their CMS (Content Management System) and have a malicious script injected into legitimate files, including “index.php” and “wp-cron.php.”
This script acts as a backdoor, which enables the malware to reinfect the site even after attempts to disinfect it. The malware is carefully designed to avoid detection and suspend redirections when a visitor is logged in as an administrator or has visited the site in the past two to six hours. The obfuscated code, which uses Base64 encoding, makes it difficult to detect.
Pumping up traffic, the malicious way
This ongoing campaign aims to generate organic traffic to websites containing Google Adsense ads. The redirections occur through Google and Bing searches and end up mostly on Q&A sites discussing Bitcoin or other cryptocurrencies.
The low-quality nature of these websites would generate little organic traffic, so the only way to pump traffic is through malicious means. This results in inflated ad views and clicks and, ultimately, inflated revenue for those behind the campaign.
According to Google Adsense documentation, this behavior is unacceptable and violates their Spam policies for Google web searches.
How to protect against this?
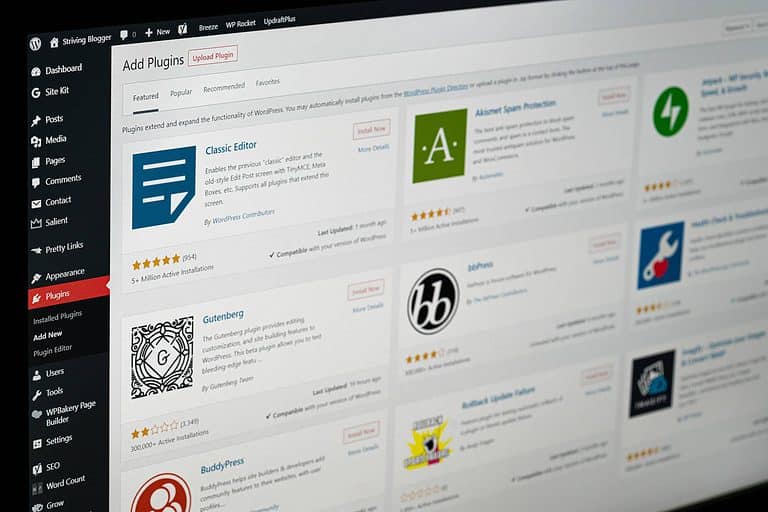
It’s unclear if Google has plans to remove the Adsense accounts associated with this scam. It also needs to be clarified how these websites are becoming infected. However, Sucuri notes that exploiting vulnerable plugins on a site is the most common method for infecting WordPress sites.
Website administrators can follow the steps provided by Sucuri to detect and remove infections. End users who find themselves redirected to one of these scam sites should close the tab and avoid clicking on any content.
To protect your website from such malicious campaigns, it’s imperative to keep your plugins and software up-to-date and to practice safe browsing habits.
Also read: Linux-based malware uses 30 WordPress exploits to inject Java Script