
Is 46% of your AI-generated code vulnerable?
As AI coding assistants become ubiquitous in enterprise development, a concerning statistic has emerged: 46% ...

As AI coding assistants become ubiquitous in enterprise development, a concerning statistic has emerged: 46% ...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

For the longest time, the technology industry has been developing a future with password-free (passwordless) ...

The UK's Pension Protection Fund, which manages a massive £39 billion in assets for nearly 300,000 members, ...

To ensure the security of online stores, Automattic, the company that manages WordPress, has announced the fo...

According to Arctic Wolf research, the Log4Shell vulnerability is still being massively abused a year after i...
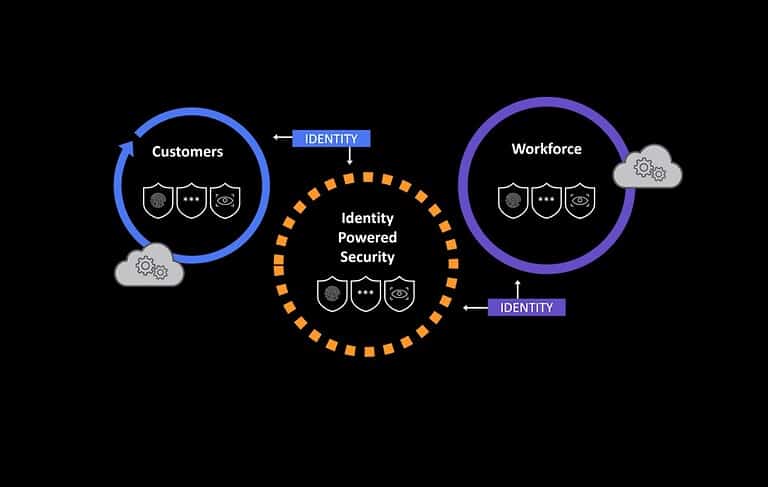
Many companies have seen their infrastructure and application landscape become more complex. This, in turn, c...

Splunk is releasing new functionality for its Security and Observability Cloud. This is to help companies bec...

Developers are being attacked by threat actors using "sophisticated typosquatting techniques". Threat acto...

The breach compromised some of Ferrari's IT systems, after which the company received a ransom demand from ha...

Only 8 percent of organizations in the Netherlands are prepared for modern cyber security threats, according ...

The move intends to bypass Microsoft security restrictions and infect more targets. Emotet is a notorious mal...