
Wiz sees big impact of AI on runtime security, but also stresses old threats
Cloud security has evolved beyond a specialized domain to encompass virtually all aspects of modern cybersecu...

Cloud security has evolved beyond a specialized domain to encompass virtually all aspects of modern cybersecu...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

Vista Equity Partners made a €4.2 billion bid to acquire KnowBe4 Vista Equity Partners will pay €24 eu...

Uber indicates that the recent cyberattack on the company was carried out by a member of the Lapsus$ group. T...

The login credentials of 25 percent of the 500 largest US organizations are for sale on the dark web, accordi...

Security researchers at VMware urge organizations to heed the rise of ChromeLoader. The malware hijacks victi...

CrowdStrike is revamping its partner program. Organizations that provide the company's security software as a...

Extended spellcheck features in Google Chrome and Microsoft Edge send sensitive form data to Google and Micro...
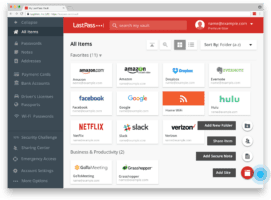
The cybercriminals behind the LastPass hack in August had access to the company's systems for four days. L...

Traditional EPP is no longer enough to protect endpoints. Organizations should all move towards EDR. Fortinet...

Tanium and Microsoft are launching joint security integrations. The collaboration focuses on integrating Micr...

A new distributed denial-of-service (DDoS) attack beat Akamai's previous record set in July. According to...